Dağ, Tamer
Loading...

Profile URL
Name Variants
Dağ, Tamer
T.,Dağ
T. Dağ
Tamer, Dağ
Dag, Tamer
T.,Dag
T. Dag
Tamer, Dag
Tamer Dağ
Da?, Tamer
T.,Dağ
T. Dağ
Tamer, Dağ
Dag, Tamer
T.,Dag
T. Dag
Tamer, Dag
Tamer Dağ
Da?, Tamer
Job Title
Doç. Dr.
Email Address
Main Affiliation
Computer Engineering
Status
Former Staff
Website
ORCID ID
Scopus Author ID
Turkish CoHE Profile ID
Google Scholar ID
WoS Researcher ID
Sustainable Development Goals
 1
1NO POVERTY
0
Research Products
 2
2ZERO HUNGER
0
Research Products
 3
3GOOD HEALTH AND WELL-BEING
1
Research Products
 4
4QUALITY EDUCATION
0
Research Products
 5
5GENDER EQUALITY
0
Research Products
 6
6CLEAN WATER AND SANITATION
0
Research Products
 7
7AFFORDABLE AND CLEAN ENERGY
6
Research Products
 8
8DECENT WORK AND ECONOMIC GROWTH
0
Research Products
 9
9INDUSTRY, INNOVATION AND INFRASTRUCTURE
2
Research Products
 10
10REDUCED INEQUALITIES
0
Research Products
 11
11SUSTAINABLE CITIES AND COMMUNITIES
2
Research Products
 12
12RESPONSIBLE CONSUMPTION AND PRODUCTION
1
Research Products
 13
13CLIMATE ACTION
1
Research Products
 14
14LIFE BELOW WATER
1
Research Products
 15
15LIFE ON LAND
0
Research Products
 16
16PEACE, JUSTICE AND STRONG INSTITUTIONS
0
Research Products
 17
17PARTNERSHIPS FOR THE GOALS
0
Research Products

This researcher does not have a Scopus ID.

This researcher does not have a WoS ID.

Scholarly Output
47
Articles
12
Views / Downloads
432/5834
Supervised MSc Theses
11
Supervised PhD Theses
5
WoS Citation Count
210
Scopus Citation Count
302
Patents
0
Projects
0
WoS Citations per Publication
4.47
Scopus Citations per Publication
6.43
Open Access Source
31
Supervised Theses
16
| Journal | Count |
|---|---|
| 29th Ieee Conference on Signal Processing and Communications Applications (Siu 2021) | 2 |
| IEEE Access | 2 |
| WMSCI 2014 - 18th World Multi-Conference on Systemics, Cybernetics and Informatics, Proceedings -- 18th World Multi-Conference on Systemics, Cybernetics and Informatics, WMSCI 2014 -- 15 July 2014 through 18 July 2014 -- Orlando -- 110235 | 2 |
| 2012 20th Signal Processing and Communications Applications Conference (SIU) | 1 |
| 2015 International Conference on Computing and Network Communications, CoCoNet 2015 -- International Conference on Computing and Network Communications, CoCoNet 2015 -- 15 December 2015 through 19 December 2015 -- Trivandrum -- 119540 | 1 |
Current Page: 1 / 6
Scopus Quartile Distribution
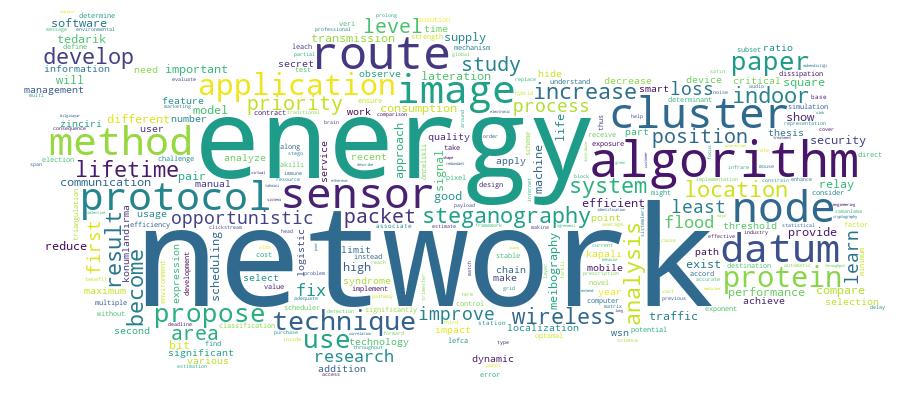
Competency Cloud
47 results
Scholarly Output Search Results
Now showing 1 - 10 of 47
Master Thesis The Performance of the Rss-Based Least Squares Lateration Algorithm for Indoor Localization(Kadir Has Üniversitesi, 2019) Barodi, Lubana; Da?, Tamer; Dağ, Tamer; Cengiz, KorhanLocalization methods have evolved over the years until the invention of the technology of global positioning system (GPS). As the technology developed and seeing that people spend most of their times in indoor environments, the need for indoor localization has arised. For localization in outdoor environments, the GPS works extremely well, but it is useless for indoor localization because the signals from the GPS satellites are too weak to penetrate the buildings. Because of that reason, the indoor positioning systems became an important research topic nowadays. There are many various methods and algorithms for locating position indoors. One of these methods is the RSS-based lateration algorithm. This method has the advantage of low cost since it uses the existing infrastructure. In addition, it provides a high level of accuracy. For these reasons, the performance of this algorithm is evaluated in this thesis. Simulation is designed to test the performance of this algorithm under different cases by using different parameters. Synthetic data is generated and used for the simulations. The algorithm is first tested with knowledge of the path loss exponent value. Then, the path loss exponent is estimated and used in the simulations. Finally, the values of RSS are estimated by using the least squares method. In this thesis, the impact of different parameters on the average error of estimated position is tested. The RSS-based least squares algorithm showed that it has a high level of accuracy which didn't exceed 2 meters in most testing areas when tested with 1 dBm noise level. It has also been shown that increasing the room size or noise level have a negative impact on the average error. However, increased path loss exponent values have a positive impact on average error. Keywords: Indoor positioning systems, Received Signal strength, Path Loss Exponent, Least Squares Lateration.Conference Object Citation - WoS: 2Citation - Scopus: 3Increasing Energy Efficiency of Wsns Through Optimization of Mobile Base Station Locations(IEEE, 2021) Abbas, Sahar S. A.; Dag, Tamer; Gucluoglu, TansalIn terms of enhancing overall energy usage, wireless sensor networks (WSNs) can run with minimal energy to extend their lifespan. Due to limited power resources, the optimal base station (BS) location could prolong the overall sensor network's lifetime. In this paper, an algorithm to find the optimal location of BS is proposed. The concept of BS virtual locations grid is used, where BS virtual locations grid within the network's area is created. To find an optimal BS location, the distances between all sensor nodes from virtual locations in the grid are considered, where one of these virtual locations will be chosen as the optimal location. Consequently, BS changes its location to another optimal location each specific number of iteration according to the number of alive sensor nodes within the network (BS mobility). The proposed algorithm is applied to the Stable Election Protocol (SEP) with two and three energy levels. Using the original SEP with two and three energy levels protocols in terms of the network's lifetime and energy consumption, the performance of the algorithm is compared. It is observed that, decreased energy consumption has been achieved, as well as the lifetime of the network has been significantly improved.Article Citation - WoS: 13Citation - Scopus: 21Improving Energy-Efficiency of Wsns Through Lefca(Sage Publications Inc, 2016) Cengiz, Korhan; Dağ, TamerWireless sensor networks (WSNs) have become an important part of our lives as they can be used in vast application areas from disaster relief to health care. As a consequence the life span and the energy consumption of a WSN have become a challenging research area. According to the existing studies instead of using direct transmission or multihop routing clustering can significantly reduce the energy consumption of sensor nodes and can prolong the lifetime of a WSN. In this paper we propose a low energy fixed clustering algorithm (LEFCA) for WSNs. With LEFCA the clusters are constructed during the set-up phase. A sensor node which becomes a member of a cluster stays in the same cluster throughout the life span of the network. LEFCA not only improves the lifetime of the network but also decreases the energy dissipation significantly.Article Citation - Scopus: 3Predicting User Purchases From Clickstream Data: a Comparative Analysis of Clickstream Data Representations and Machine Learning Models(IEEE-Inst Electrical Electronics Engineers inc, 2025) Tokuc, A. Aylin; Dag, Tamer; Aylin Tokuc, A.Predicting purchase events from e-commerce clickstream data is a critical challenge with significant implications for optimizing marketing strategies and enhancing customer experience. This study addresses this challenge by systematically evaluating and comparing multiple data representations - aggregated session attributes, recent user actions, and hybrid combinations - which bridges gaps in the existing literature and demonstrates the superiority of hybrid approaches. Unlike prior research, which typically focuses on single representations, our approach combines aggregated session-level summaries with granular, sequential user actions to capture both long-term and short-term behavioral patterns. Through comprehensive experimentation, we compared multiple machine learning models, including LightGBM, decision trees, gradient boosting, SVC, and logistic regression, using real-world e-commerce clickstream data. Notably, the hybrid representation with LightGBM achieved superior predictive performance, significantly outperforming alternative methods. Feature importance analysis revealed key factors influencing purchase likelihood, such as time since the last event, session duration, and product interactions. This study provides actionable insights into real-time marketing interventions by demonstrating the practical utility of hybrid data representations and efficient tree-based models. Our findings offer a scalable and interpretable framework for e-commerce platforms to enhance purchase predictions and optimize marketing strategies.Conference Object Dynamic Priority Packet Scheduler With Deadline Considerations (dpd)(INT INST Informatics & Systemics, 2010) Dağ, TamerProviding quality of service (QoS) to applications with different traffic characteristics based on their needs is an important research area for today's and tomorrow's high speed networks. Various techniques have been proposed to achieve good QoS for diverse application types. Among these techniques packet scheduling algorithms decide on how to process packets at network nodesDoctoral Thesis A Novel Communication Method for Constrained Iot Devices(Kadir Has Üniversitesi, 2022) Kocatekin, Tuğberk; Tamer Dağ; Cafer Çalışkan; Dağ, Tamer; Çalışkan, CaferInternet of Things (IoT) is becoming an established part of life by interconnecting billions of devices in diverse areas such as healthcare, smart homes, industries, etc. However, these devices are limited in memory, energy and computational capabilities. Being constrained prevents them from applying complex cryptographic encryption algorithms which leads to lack of security and therefore lack of privacy. As a solution, we propose a novel secret sharing scheme based on underlying protocols of visual cryptography to provide a low-cost and secure communication method for constrained IoT devices. Generally, when a device wants to communicate with an outer party, it does so by itself or by using a mediary such as a central hub or gateway; which leads to single point of failure. As a solution, we propose a method where devices collaborate each other and therefore divide the responsibility into multiple, instead of one. We propose two different models: n-out-of-n and k-out-ofn. In the first model, there is a complete graph where every device is connected to each other. Instead of the original sender, every other device work collaboratively to communicate with the outer party. In the second model, the network is realized as an n-regular graph where a single node has n number of neighbors, which collaborates with each other and here the responsibility is divided into n devices. Results show that this scheme is applicable to constrained devices.Conference Object Citation - Scopus: 4Routing With (p-Percent) Partial Flooding for Opportunistic Networks(2010) Erdoğan, Mustafa; Günel, Kadir; Koç, Tuğba; Sökün, Hamza Ümit; Dağ, TamerOpportunistic networks are one of the fast developing research areas in mobile communications. Under opportunistic networks mobile nodes try to communicate with other nodes without any prior information and knowledge about the network topology. Furthermore the network topologies are dynamic and can rapidly change. In addition communication under opportunistic networks can be erratic thus routes between a source node and a destination node sometimes might not exist. These issues would make traditonal routing approaches insufficient and unusable for opportunistic networks. In this paper a new routing approach for opportunistic networks is proposed. The approach is called is p% partial flooding algorithm. With flooding it is possible to reach a destination node with the minimum number of hops and minimum end-to-end delay. But the major disadvantage of flooding is the excessive usage of the network resources. With p% partial flooding algorithm the aim is to decrease the network traffic by randomly selecting neighbor nodes and routing traffic through them. This paper explains these two approaches (flooding and p% partial flooding) and compares their performance through various simulations. It is observed that p% partial flooding can result in the same benefits of flooding while decreasing the network traffic. Copyright © 2010 The authors.Master Thesis Developing Novel Techniques for Spatial Domain Lsb İmage Steganography(Kadir Has Üniversitesi, 2019) Shehzad, Danish; Dağ, TamerSteganography is one of the most noteworthy information hiding mechanism, which is used as an alternative to cryptography in order to provide adequate data security. Image steganography is one of the key types of steganography where a message to be transmitted is hidden inside a cover image. The most commonly used techniques for image steganography rely on LSB Steganography. In this thesis, new techniques are developed for LSB image steganography to achieve maximum security, optimal data capacity along with provisioning of efficient steganography mechanism. In the first part of this work, a novel technique based on pairs matching is developed for LSB image steganography. In this technique MSBs along with LSBs are used in a delicate method for data hiding for the first time. The message bits from the secret information are compared with all defined pixel pairs and replace the least two significant bits with respective matched pair number. This technique shows good quality of stego image along with adequate peak signal to noise ratio and provides high payload of secret message. In the second part, threshold-based LSB image steganography technique is developed. This technique also works in spatial domain and categorizes the pixels based on threshold defined categories. Maximum four bits and minimum one bit is embedded in pixel based on its category. The prominence in THBS is on security and payload as it uses bits proficiently for data embedding. ETHBS allows efficient execution of the algorithm along with provisioning of optimal security. In the last part 1LSB Image steganography technique based on blocks matrix determinant is developed. It is a technique in which data is embedded by making minimal changes in image pixels. This technique is 1LSB substitution technique that works on matrix determinant of 2 by 2 blocks of image pixels. This technique ensures high PSNR and ensures good quality of stego image.Master Thesis Design and Implementation of a Mobile Prescription System With Patient-Healthcare Professional Interaction(Kadir Has Üniversitesi, 2015) Öztürk, Çağdaş Egemen; Dağ, TamerIn this thesis, a mobile prescription reminder and scheduling system application with patient-healthcare professional interaction is designed and implemented. By using the application, different types of users are able to create and manage prescriptions and are reminded to take the medication based on the prescription data. Besides, users are able to reach the prospectuses of the drugs. One of the most important functionality of the application is to provide patient-healthcare professional interaction. By using the application, healthcare professionals can assign prescriptions to their patients and they can also monitor their medicine compliance. Since the medicine compliance is very important to have an effective treatment, the main goal of this application is to help people to take their medicines on time and find the prospectus information of the drugs easily by using their mobile phones.Conference Object An Energy Efficient Routing Algorithm (x-Centric Routing) for Sensor Networks(INT INST Informatics & Systemics, 2011) Ataç, Göktuğ; Dağ, TamerRecent developments in wireless communications and electronics technologies have enabled the progress in low cost sensor networks. Sensor networks differ from traditional networks in several ways such as the severe energy constraints redundant low-rate date and many-to-one flows that the sensor networks require. One of the major challenges facing the design of a routing protocol for Wireless Sensor Networks (WSNs) is to find the most reliable path between the sources and the sink node by considering the energy awareness as an essential design parameter. This paper introduces a new routing protocol called as X-Centric routing by considering the above parameters. Under the X-Centric routing the decision making mechanism depends on the capacity of the sink node by switching between address-centric routing (AC-Routing) and data-centric routing (DC-Routing). The design tradeoffs between energy and communication overhead savings in these routing algorithms have been considered by considering the advantages and performance issues of each routing algorithm.

