Dağ, Hasan
Loading...

Profile URL
Name Variants
D., Hasan
Dağ, HASAN
DAĞ, HASAN
Hasan, Dag
HASAN DAĞ
Hasan DAĞ
DAĞ, Hasan
Daǧ H.
Hasan Dağ
Dağ, H.
Dağ,H.
D.,Hasan
Dağ, Hasan
Dag H.
Dag,H.
Dağ H.
Dag,Hasan
Dag, Hasan
H. Dağ
Da?, Hasan
Dağ, HASAN
DAĞ, HASAN
Hasan, Dag
HASAN DAĞ
Hasan DAĞ
DAĞ, Hasan
Daǧ H.
Hasan Dağ
Dağ, H.
Dağ,H.
D.,Hasan
Dağ, Hasan
Dag H.
Dag,H.
Dağ H.
Dag,Hasan
Dag, Hasan
H. Dağ
Da?, Hasan
Job Title
Prof. Dr.
Email Address
Main Affiliation
Management Information Systems
Status
Current Staff
Website
ORCID ID
Scopus Author ID
Turkish CoHE Profile ID
Google Scholar ID
WoS Researcher ID
Sustainable Development Goals
11
SUSTAINABLE CITIES AND COMMUNITIES

2
Research Products
10
REDUCED INEQUALITIES

0
Research Products
9
INDUSTRY, INNOVATION AND INFRASTRUCTURE

16
Research Products
12
RESPONSIBLE CONSUMPTION AND PRODUCTION

0
Research Products
2
ZERO HUNGER

0
Research Products
3
GOOD HEALTH AND WELL-BEING

2
Research Products
13
CLIMATE ACTION

0
Research Products
7
AFFORDABLE AND CLEAN ENERGY

2
Research Products
5
GENDER EQUALITY

0
Research Products
6
CLEAN WATER AND SANITATION

0
Research Products
8
DECENT WORK AND ECONOMIC GROWTH

2
Research Products
16
PEACE, JUSTICE AND STRONG INSTITUTIONS

0
Research Products
4
QUALITY EDUCATION

2
Research Products
15
LIFE ON LAND

3
Research Products
1
NO POVERTY

0
Research Products
14
LIFE BELOW WATER

1
Research Products
17
PARTNERSHIPS FOR THE GOALS

3
Research Products

Documents
85
Citations
946
h-index
13

Documents
45
Citations
225

Scholarly Output
101
Articles
19
Views / Downloads
98/0
Supervised MSc Theses
26
Supervised PhD Theses
3
WoS Citation Count
448
Scopus Citation Count
859
WoS h-index
8
Scopus h-index
12
Patents
0
Projects
0
WoS Citations per Publication
4.44
Scopus Citations per Publication
8.50
Open Access Source
53
Supervised Theses
29
| Journal | Count |
|---|---|
| Computers & Security | 2 |
| TURKISH JOURNAL OF ELECTRICAL ENGINEERING & COMPUTER SCIENCES | 2 |
| 2010 International Conference on Power System Technology | 2 |
| UBMK 2023 - Proceedings: 8th International Conference on Computer Science and Engineering -- 8th International Conference on Computer Science and Engineering, UBMK 2023 -- 13 September 2023 through 15 September 2023 -- Burdur -- 193873 | 2 |
| UBMK 2024 - Proceedings: 9th International Conference on Computer Science and Engineering -- 9th International Conference on Computer Science and Engineering, UBMK 2024 -- 26 October 2024 through 28 October 2024 -- Antalya -- 204906 | 2 |
Current Page: 1 / 11
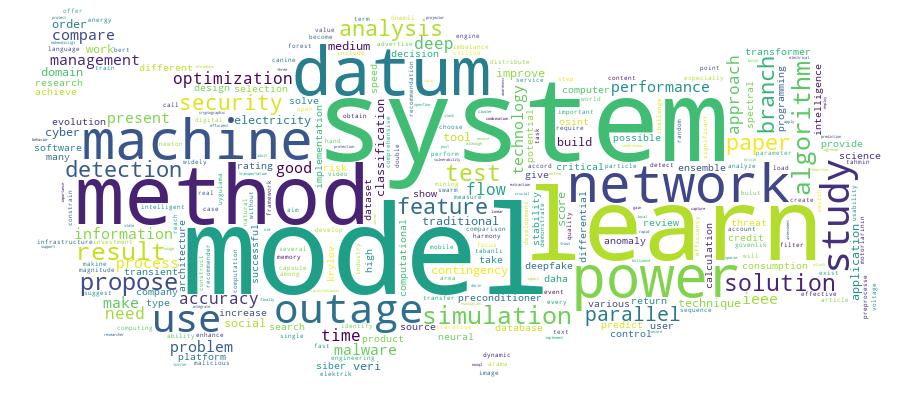
Competency Cloud